Back in January I had reported on the hacking of HD-DVD protection by improper key management. AACS, makers of the DRM protecting the new format, vowed to try to shut down BackupHDDDVD, which is instrumental to some part of the cracking process. At the time I thought it was likely to be the last we would hear about this topic, after all, cracked protection is hardly news, is it? Once the how-to had been posted in Ed Felten's blog, the game was up. Or so I thought...
In order to understand the cracking process, we need to understand keys. Felten explains it best, so here he goes:
"In AACS, each player device is assigned a DeviceID (which might not be unique to that device), and is given decryption keys that correspond to its DeviceID. When a disc is made, a random “title key” is generated and the video content on the disc is encrypted under the title key. The title key is encrypted in a special way that specifies exactly which devices’ decryption keys are able to extract the title key, and the result is then written into a header field on the disc.
When a player device wants to read a disc, the player first uses its own decryption keys (which, remember, are specific to the player’s DeviceID) to extract the title key from the disc’s header; then it uses the title key to unlock the content."
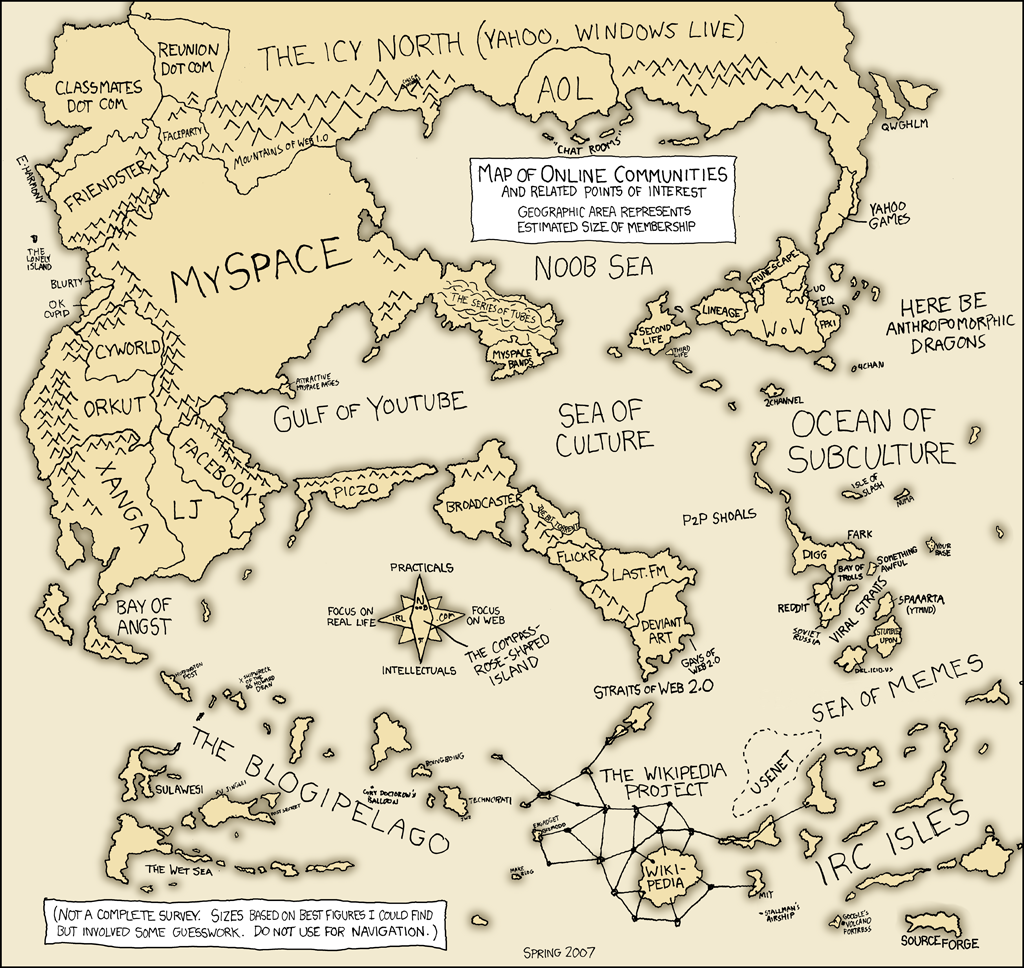
However, January's vulnerability was limited, as it could not decrypt the title's key, it was only a player key, which would be useless by itself. Suggestions were made to have a title key database that cracking software could access, but as far as I know it was not implemented. That was the state of play until yesterday, when a key was released to the public which allegedly can be used to decrypt most existing titles. Apparently, this is a processing key, something akin to a master key. I have not been able to find the first source of the key, although some sites have posted a link to a removed WordPress blog here. The earliest post I could find in this meme is here. Perhaps in the days of Web 2.0, it is impossible to find sources. Anyway, what we know for sure is that someone posted this somewhere (vagueness is also very web 2.0):
"Spread this number. Now.
09 F9 11 02 9D 74 E3 5B D8 41 56 C5 63 56 88 C0. It's the HD-DVD processing key you can use to decrypt and play most HD-DVD movies in Linux. Movie studios are going ballistic over this leak, so Digg the story up and make it reach the front page."
This was like DeCSS all over again, but this time with blogs, YouTube, Digg and the whole force of a meme-churning machine. In other words, AACS does not stand a chance. That doesn't mean they did not try! Apparently the number made front page of Digg, who then received a Cease & Desist letter and decided to remove the stories and even cancel user's accounts. Needless to say, the slightest whiff of censorship sent the copyfight warriors on overdrive, and we had a t-shirt (pictured), replication in countless blogs, and even a song uploaded on YouTube. Some of the discussions in Slashdot and Wired have been worth reading as sociological examples of slighted self-righteous geekdom. I can imagine this repeated in chat-rooms across the world:
"Replicate this number, it allows you to copy your HD-DVDs"
"But, I don't own any"
"Doesn't matter man, they're trying to censor us!"
Digg realised they were losing the good will of geekdom, so they posted a "we hear ya", together with the dreaded number on the title. They have decided to "go down fighting" and side with the rebelling masses.
I may be forgiven for being my cynical self, but I must admit that I'm getting slightly suspicious about this whole affair, I'm missing some very basic information in order to make sure that this is a legitimate issue. Here are some problems that I have with the news:
- Where is the original post? Has it really been taken down?
- The earliest key replication seems to come from a meme post designed to anger the masses. No, you cannot copyright numbers, but keys may be protected as part of an effective technological protection measure.
- AACS has not made any official declaration that it's pursuing infringers, something that they have done in the past.
- I would like to see Digg's cease-and-desist letter, it seems to me like lawyers for the industry moved incredibly fast.
- There's something about the whole story that smells like urban legend to me. The meme has spread too fast in order to get accurate information.
- Has anyone actually tried to use the key?
It's possible that my suspicions are misplaced. If that is the case, AACS may have committed the biggest blunder by trying to suppress the key; the level of dissemination is such that it will be impossible to recall it. This may prove to be a case study of how useless cease-and-desist may become in the Web 2.0 era. Even if the story proves to be a clever hoax, copyright owners should heed the lesson.
Update. Some interesting replication strategies from David Berry:
But I still haven't seen any first-hand report that anyone has actually used the key to crack an HD-DVD.
Update 2: Chilling effects has posted
the AACS C&D letter to Google, so I guess that makes it official, the key seems legit. If AACS wants to take it down, there must be a reason.
"Ladran Sancho, señal que caminamos".
Update 3: Fred von Lohmann from EFF
has posted a warning against posting the key.

 del.icio.us
del.icio.us